SSH
Secure Shell (SSH) is a cryptographic network protocol for secure data communication, remote command-line login, remote command execution, and other secure network services between two networked computers that connects, via a secure channel over an insecure network, a server and a client (running SSH server and SSH client programs, respectively).
The best-known application of the protocol is for access to shell accounts on Unix-like operating systems, but it can also be used in a similar fashion for accounts on Windows.
It was designed as a replacement for Telnet and other insecure remote shell protocols, which send information, notably passwords, in plaintext, rendering them susceptible to interception and disclosure using packet analysis.
The encryption used by SSH is intended to provide confidentiality and integrity of data over an unsecured network, such as the Internet.
The SSH I/O Server implements the SSH-2 version of the protocol, and supports remote command execution and the SCP protocol for bidirectional file transfer. It uses HSYCO data points to execute commands and return command status, making it easy to use the SSH protocol in EVENTS, as well as JavaScript and Java.
The SSH I/O Server establishes a single SSH connection to the server, using password-based authentication, and creates individual sessions to execute single commands.
![]() Commands are executed sequentially, not in parallel.
Commands are executed sequentially, not in parallel.
Contents
SSH Remote Server Configuration
The remote system should be configured to accept the SSH connection from the HSYCO server using the username and password defined in the I/O Server’s options.
If you need to execute operating system’s commands with superuser privileges (with the sudo program), the remote user name defined with the user option in the SSH I/O Server configuration must be allowed to execute “sudo” commands without asking for a password.
For example, if the user is hsyco, you could add the line:
hsyco ALL=(ALL:ALL) NOPASSWD: ALL
at the end of the /etc/sudoers file (use the visudo command to edit the /etc/sudoers file).
HSYCO Configuration
Options
| ID | Default | Values | Description |
|---|---|---|---|
| stdout | true | true | when a remote command is executed, generate IO events containing the command's standard output and standard error streams |
| false | do not generate IO events of the command's output and error streams |
Datapoints
| ID | Value | R/W | Description |
|---|---|---|---|
| connection | online | R | connection established |
| offline | R | HSYCO can't connect to the remote SSH server | |
| exec | command string | W | executes the command passed as value |
| exit status | R |
| |
| err | error stream | R | the executed command standard error stream, with lines separated by "<br>", or an empty string if the command's error stream is empty |
| out | error stream | R | the executed command standard output stream, with lines separated by "<br>", or an empty string if the command's output stream is empty |
| get | source destination | W | retrieves the remote source file and writes it locally to the destination path name. The source and destination string in value should be separated by one or more spaces. Always use the "/" character as path separator. Use "\" as the escape character if the file names have spaces. The destination directory must exist and cannot be outside of the HSYCO's base directory, or the command will fail. If the destination name doesn't have a path, the file will be written to the HSYCO's base directory |
| number of transferred bytes, or "error" | R |
| |
| put | source destination | W | copy the local source file to the remote server's destination path name. The source and destination string in value should be separated by one or more spaces. Always use the "/" character as path separator. Use "\" as the escape character if the file names have spaces. The source directory must exist and cannot be outside of the HSYCO's base directory, or the command will fail. If the source name doesn't have a path, the file will be written to the HSYCO's base directory. The file will be saved to the remote server with 600 (owner's only read and write) permission |
| number of transferred bytes, or "error" | R |
|
![]() The exec, err, out, get and put data points will trigger the IO events at the end of the command's execution even if the value is not changed. This allows you to easily intercept the exit status and other return information.
The exec, err, out, get and put data points will trigger the IO events at the end of the command's execution even if the value is not changed. This allows you to easily intercept the exit status and other return information.
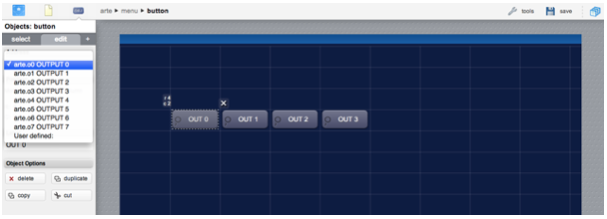
User Interface
When using the default settings of the Arteco I/O Server, all output pins are available in the Project Editor and can be easily associated to any control button of the Web interface.
You can also set the inputdiscovery option in order to associate control buttons to the module’s inputs: the control buttons will show the input status, and have no effect when pressed.
Release Notes
3.3.0
- initial release
HSYCO and Home Systems Consulting are registered trademarks of Home Systems Consulting SpA. Java and JavaScript are registered trademarks of Oracle and/or its affiliates. ARTECO is a registered trademark of Arteco Srl. Other products or company names can be trademarks or registered trademarks of other companies and are used for demonstrative purposes only, with no violation intent.